Cybersecurity Myth Busted: We’re Secure
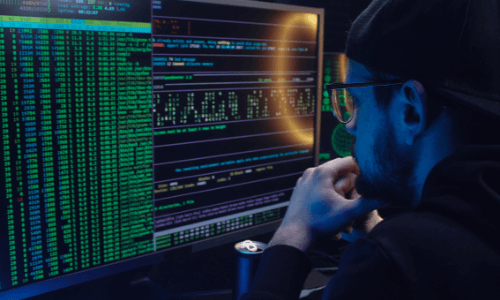
There is no such thing as "secure vs insecure". That's not how security works. The adversaries only need to find the one risk you missed (or didn't know about).
Cybersecurity Myth Busted: We’ll Just Pay the Ransom
Paying the ransom will not immediately stop the attack and restore your systems. You still have to remove the initial attack vectors and infections.
Cybersecurity Myth Busted: We’re Not a Target
Since every organization has something valuable it must protect, the reality is that every organization is a potential target for extortion-related attacks.
Cybersecurity Myth Busted: Tools Are the Solution
Trying to secure an organization, data, or an environment does not revolve around tools. Instead, they must be managed with ongoing processes and procedures.
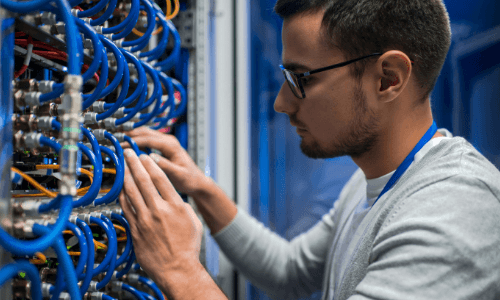
Part-Time Staff Cannot Monitor and Manage Your Security
Security isn't 9-5. You have concerns, risks, and attacks 24/7/365. Adversaries work around the clock. Therefore, your security also needs constant attention.
Cybersecurity Myth Busted: Security Can Be Managed by IT
IT focuses on building and running systems to enable business. But Security asks if the systems are secure, if they can break them, and how they can be misused.
Beware of These 6 Common Gaps in Environmental Security
Of the hundreds of ways an environment or data can be breached, these are six of the most common gaps we have been seeing in client environments today.
Current and Future Challenges with Hybrid and Remote Work Models
Here are some current and anticipated future security risks we see with the hybrid work model, along with some high-level recommendations on remediation.
Cybersecurity Myth Busted: Security is the Final Goal
When you think about your security programs, do you think of security as the final goal? If so, we debunk three claims we often hear to justify that stance.
Featured Content
Subscribe to our Newsletter
Stay informed on the latest technology news and trends